Threat breakdown: Remote access and credential dumping


Throughout the course of a day, the Todyl MXDR team reviews security alerts, investigates threats, and hunts for the unknown all on a recurring basis on behalf of their customers. While many suspicious behaviors are reviewed and remediated, it’s important to dissect some attacks to better understand the techniques used and ensure there are robust detections in place to highlight anything suspicious.
A recent incident involved the use of multiple techniques which when chained together, could have been disastrous for the victim's organization. This organization was leveraging Todyl SIEM, and a third-party anti-virus application. The incident started with a few “low” severity alerts all bucketed together, which always has our analysts on high alert. Low-severity alerts are generally not a major concern individually. But, when multiple low-severity alerts are triggered for the same host or user, that increases the awareness of our analysts that prompts further investigation.
Digging into the alerts
The following alerts were present:
- Enumeration of Administrator Accounts
- Credential Access via Known Utilities
- RDP Enabled via Registry
- Credential Acquisition via Registry Hive Dumping
The alerts, individually, are not as concerning. The first of which “Enumeration of Administrator Accounts” is common to see amongst various networks. Remote management and monitoring tools, commonly used by managed service providers, enumerate user groups, software installations, and other system characteristics regularly.
cmd /c net group "domain admins" /domain
The above command is straightforward. It uses the NET.exe command to list the users in the "domain admins" group within the target domain. This command is different from the usual commands seen in this type of alert. By using “cmd /c”, a new command prompt process is created to run the command. This method is commonly used by threat actors when executing commands through a remote shell.
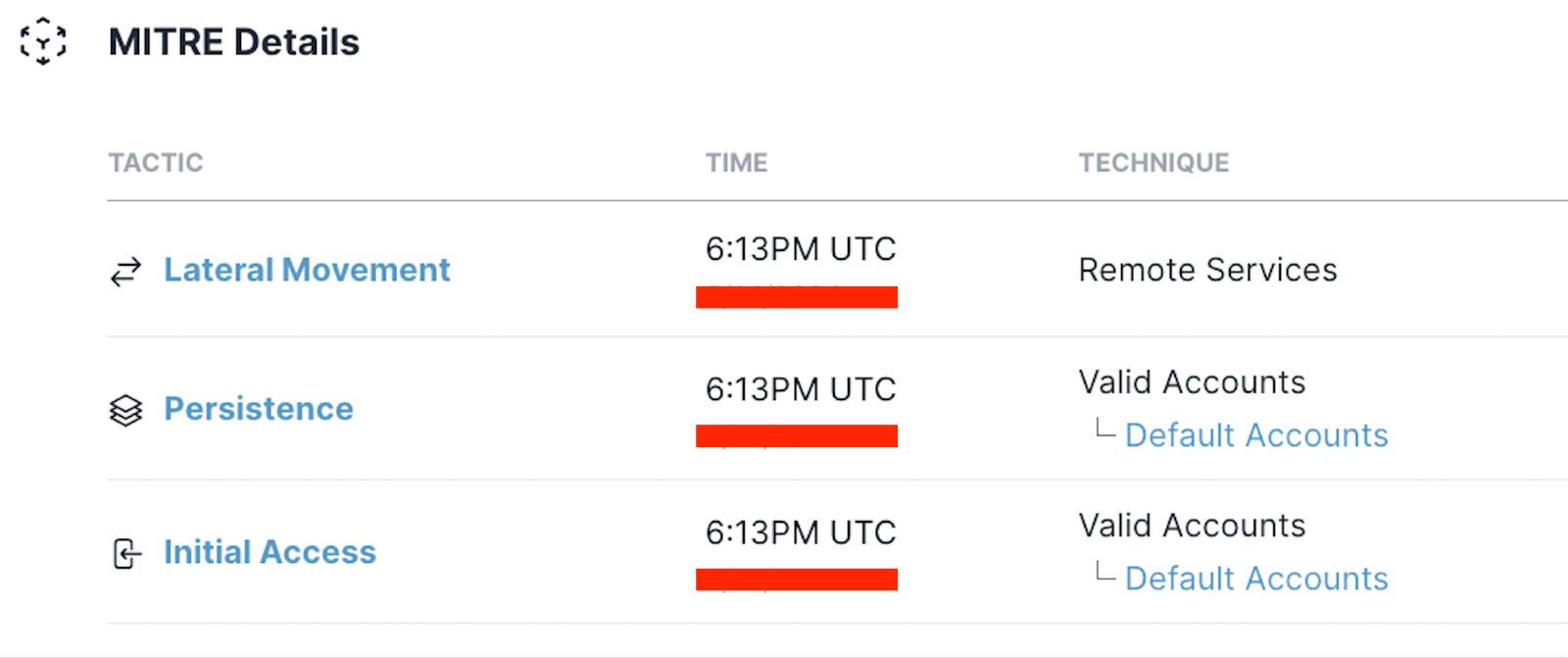
Mapping to MITRE
When reviewing the MITRE tactics for these commands, it’s clear that these activities are all commonly associated with initial access and lateral movement.
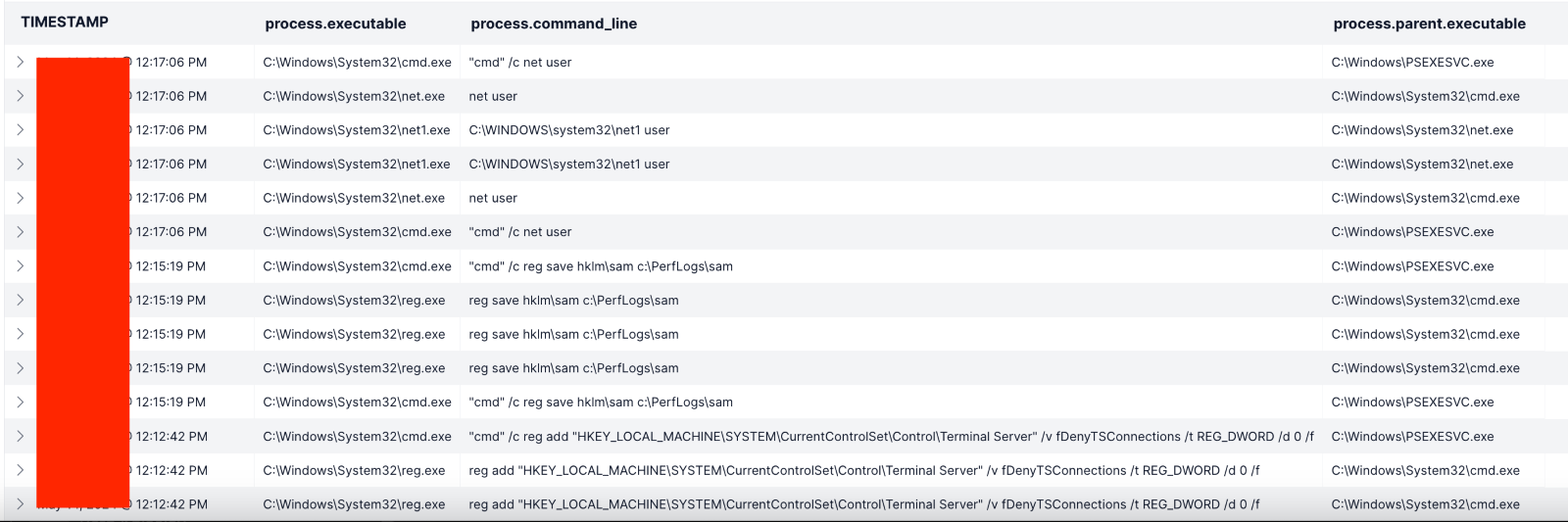
The above image shows an outline of the commands run in a 5-minute time span. Several other alerts led to the MXDR team performing a host isolation of this device. The threat actor appeared to have compromised a user account and was not only enumerating administrator accounts but was actively attempting to dump credentials and enabling Remote Desktop via the registry.
By using the “reg save” command, the threat actor was attempting to export the “HKLM:\SAM” hive and save it to “C:\PerfLogs\sam”. This file can be leveraged by multiple credential dumping toolkits to escalate their privileges and move laterally throughout the network.
Addressing the issue with haste
With the threat actor isolated from the host in question, the investigation continued to identify the source of the compromise. With Todyl Endpoint Security enabled, many of the common methods for threat actors to gain access are prevented, stopping them in their tracks. However, not every environment has Endpoint Security active or in Prevention Mode. So, it's up to the MXDR team to collaborate with our partners using the access and data available to them.
By reviewing successful logon activity for the host and user involved in the above alerts, it was identified that an unknown device on the network had deployed a rogue version of “ScreenConnect”, a remote access utility via a commonly abused administrator utility named “PSEXEC”. The threat actor had compromised a user account and was using the stolen credentials to conduct their activities.
The Todyl MXDR team contacted the impacted customer and provided detailed remediation steps, as well as assisted in ensuring the Todyl Endpoint Security module was deployed to clean up any remaining artifacts. After the host and user account was verified to be in good standing, the isolation was removed, and the case was closed out.
While this attack was not incredibly sophisticated, it highlights the need for foundational security controls. By leveraging the Todyl Security Platform, the incident was investigated and remediated quickly, however if this organization did not have MXDR, the result from these attacks is often ransomware, theft of sensitive information, or destruction of data. With response and remediation in less than an hour, the threat actors were unsuccessful in their attempts to expand their footprint.
Some of the ongoing guidance provided to our impacted customer includes:
- Ensuring the Todyl SGN Agent is installed across the entire network
- Ensuring EDR is activated and in Prevention mode
- Apply the principal of least privilege and restrict user accounts to only the permissions they require
- Reset the impacted user account credentials
- Apply LanZeroTrust to restrict lateral movement and segment the network
Timeline of events
As you can see in the timeline below, MXDR acted rapidly between detection and remediation to isolate the host and rectify the issue. See more of MXDR in action; read this case study of how MXDR prevented an ongoing malware attack.

Cybersecurity Readiness Assessment
Analyze your operational readiness and get instant assessment-driven insights to strengthen your security posture.
Stay on the Cutting Edge of Security
Subscribe to our newsletter to get our latest insights.



