Identity Threat Detection & Response
Todyl ITDR delivers critical, 24/7 protection from identity-based attacks, privilege abuse, and cloud security threats for organizations of all sizes.
Why ITDR?
Identity-based threats are one of the most dangerous attack vectors for any organization, but small to mid-sized organizations rarely have the resources and expertise to detect and respond to attacks. Todyl ITDR protects organizations of all sizes from identity-based attacks around the clock.
Todyl ITDR Delivers
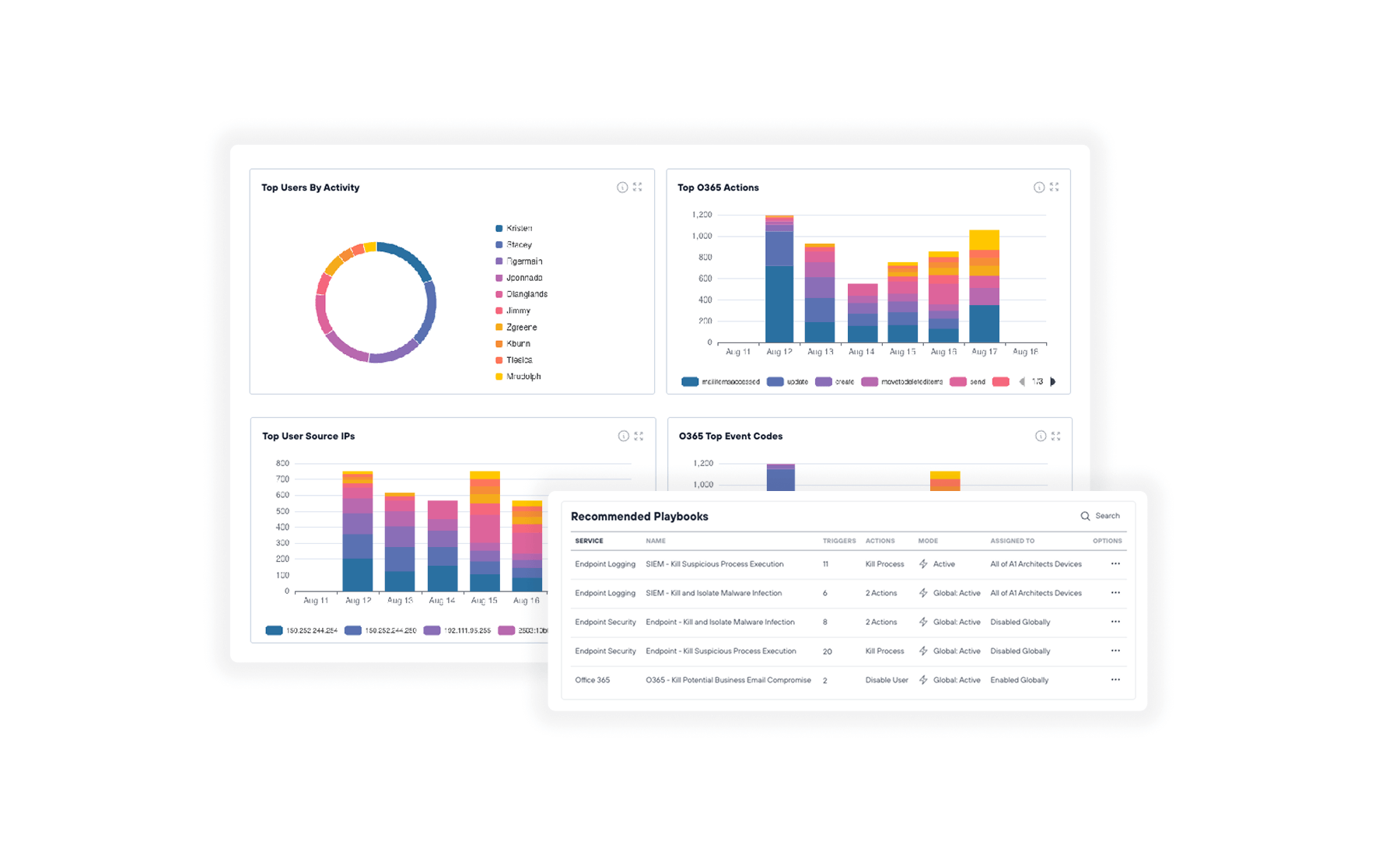
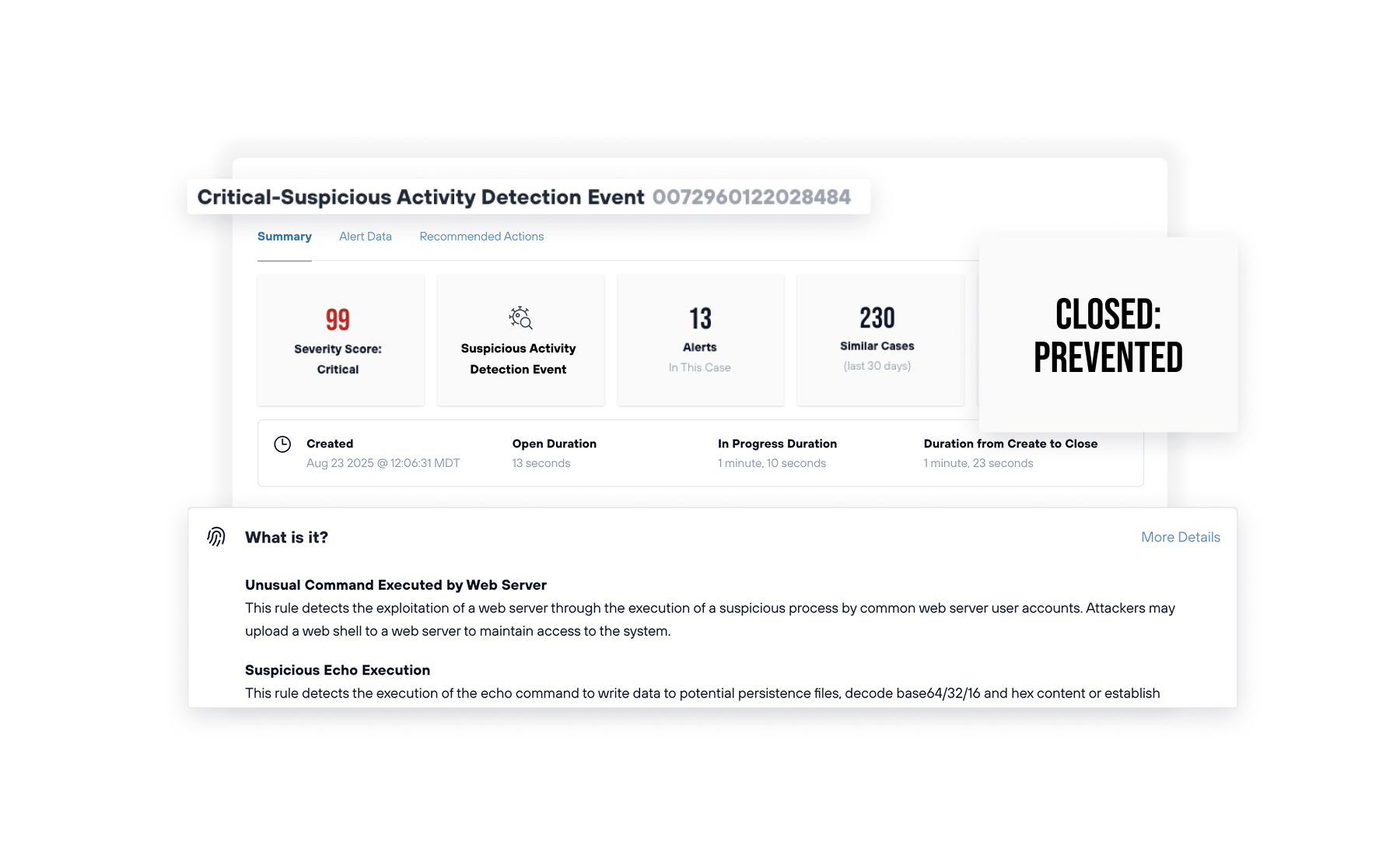
Todyl’s MXDR team delivers 24/7 expert ITDR services for G-Suite, Microsoft 365, and Azure environments, monitoring for anomalous identity usage and account access, at a fraction of the cost of implementing an in-house program.
Continuous monitoring and protection of cloud identities
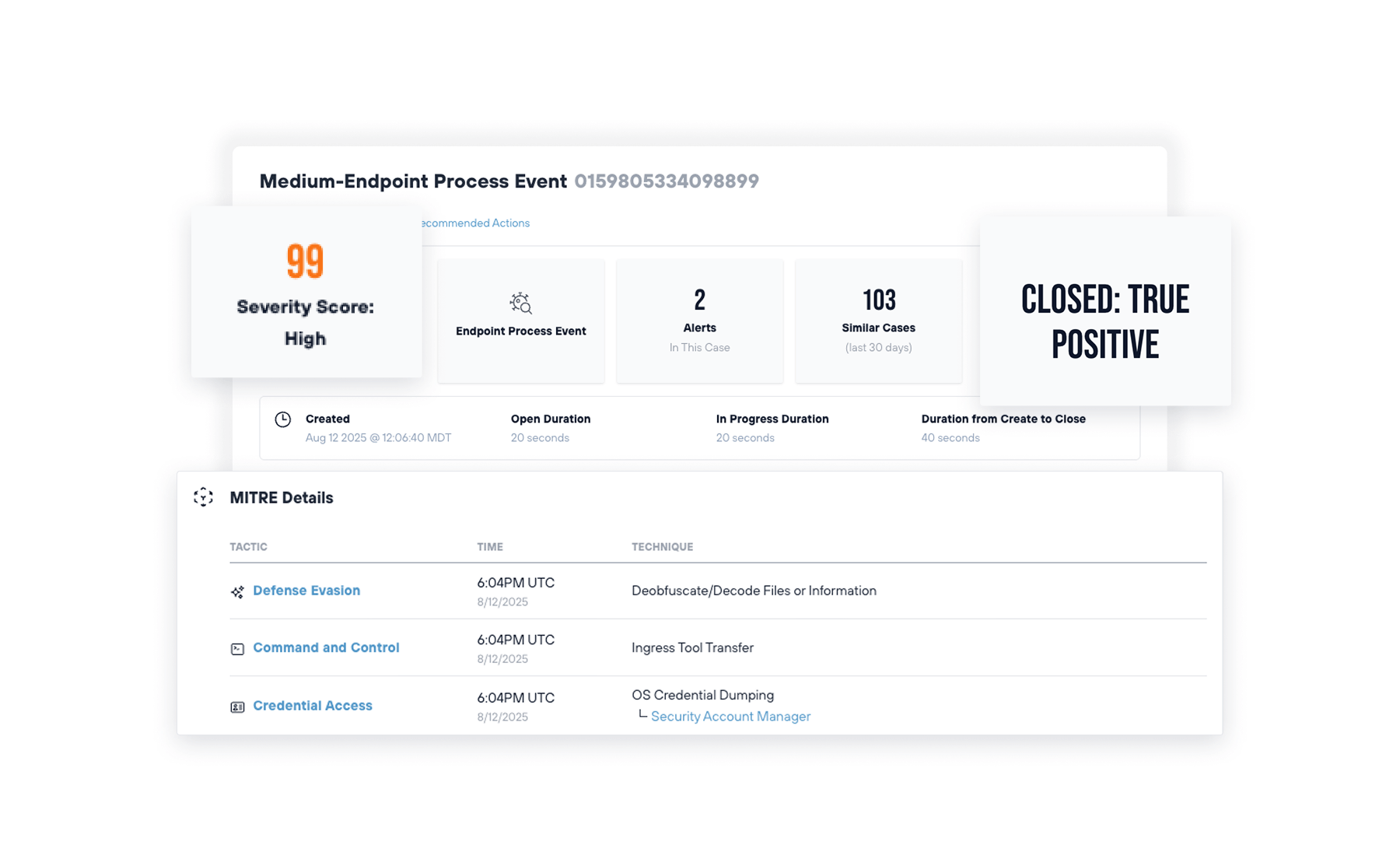
Rapid containment of advanced attacks (ATOs, AitM, etc.)
Anomalous account access and usage detection

Herd immunity across all Todyl partners (BECs, Ransomware, etc.)
Testimonials
Get started with ITDR today