Powerful & Intuitive GRC Software
Todyl GRC (Governance, Risk & Compliance) streamlines cybersecurity governance, strategic risk management, and continuous compliance and insurability with a full suite of centralized data collection, policy documentation, and operating frameworks.
Enterprise GRC Without the Complexity
Todyl GRC delivers organizational alignment and demonstrability for insurance and compliance requirements. Easy access to documented policies, operating frameworks, and automated tools streamline mapping and demonstrating cybersecurity efficacy, risk analysis, and compliance and insurance adherence.
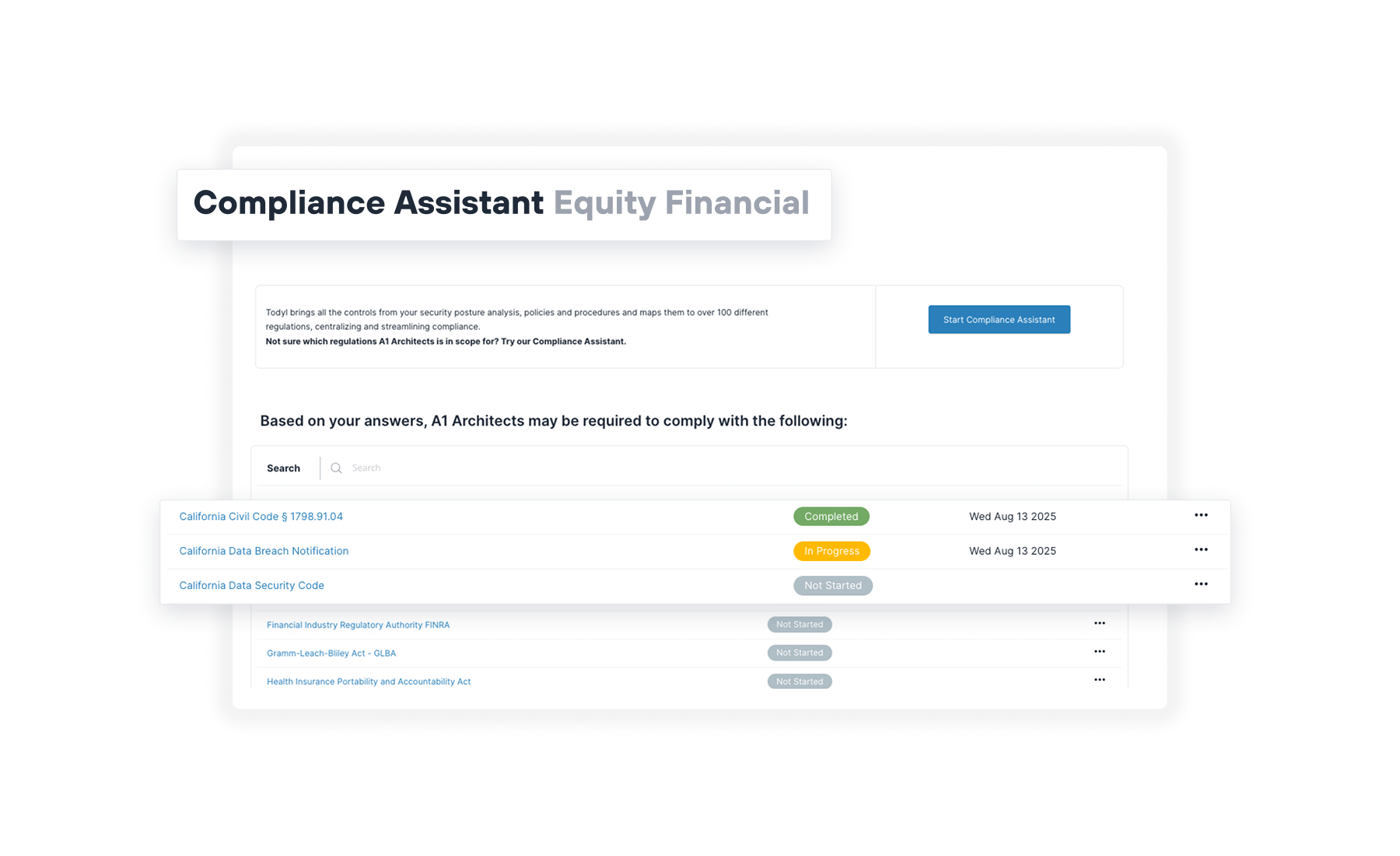
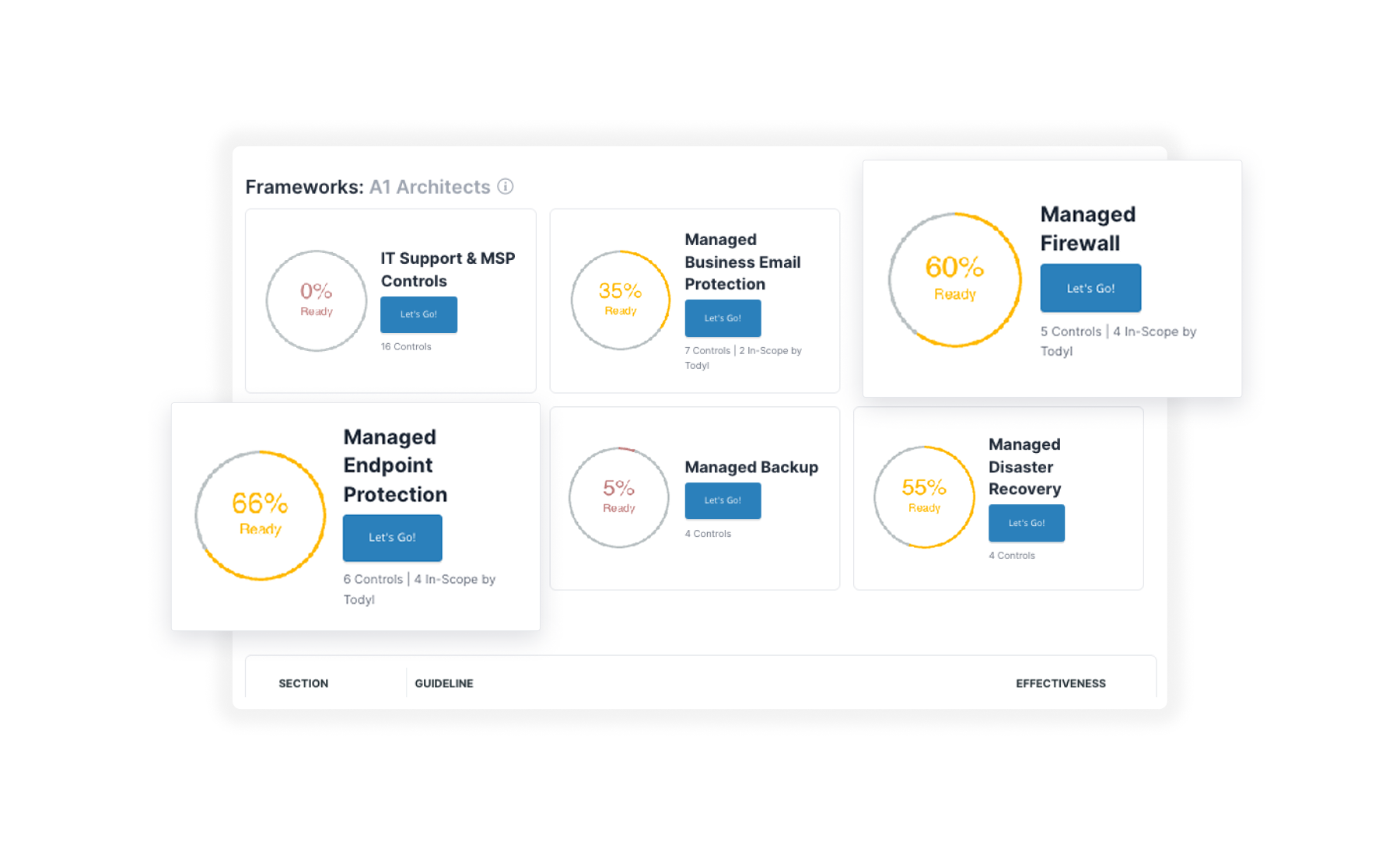
Automated compliance mapping
Quickly identify which regulations and frameworks are in scope with Todyl's easy-to-use Compliance Assistant:
- Pinpoint specific required regulations and relevant guidelines
- Align by geography, industry vertical, company size, and more
- Map existing programs to individual controls and eliminate gaps
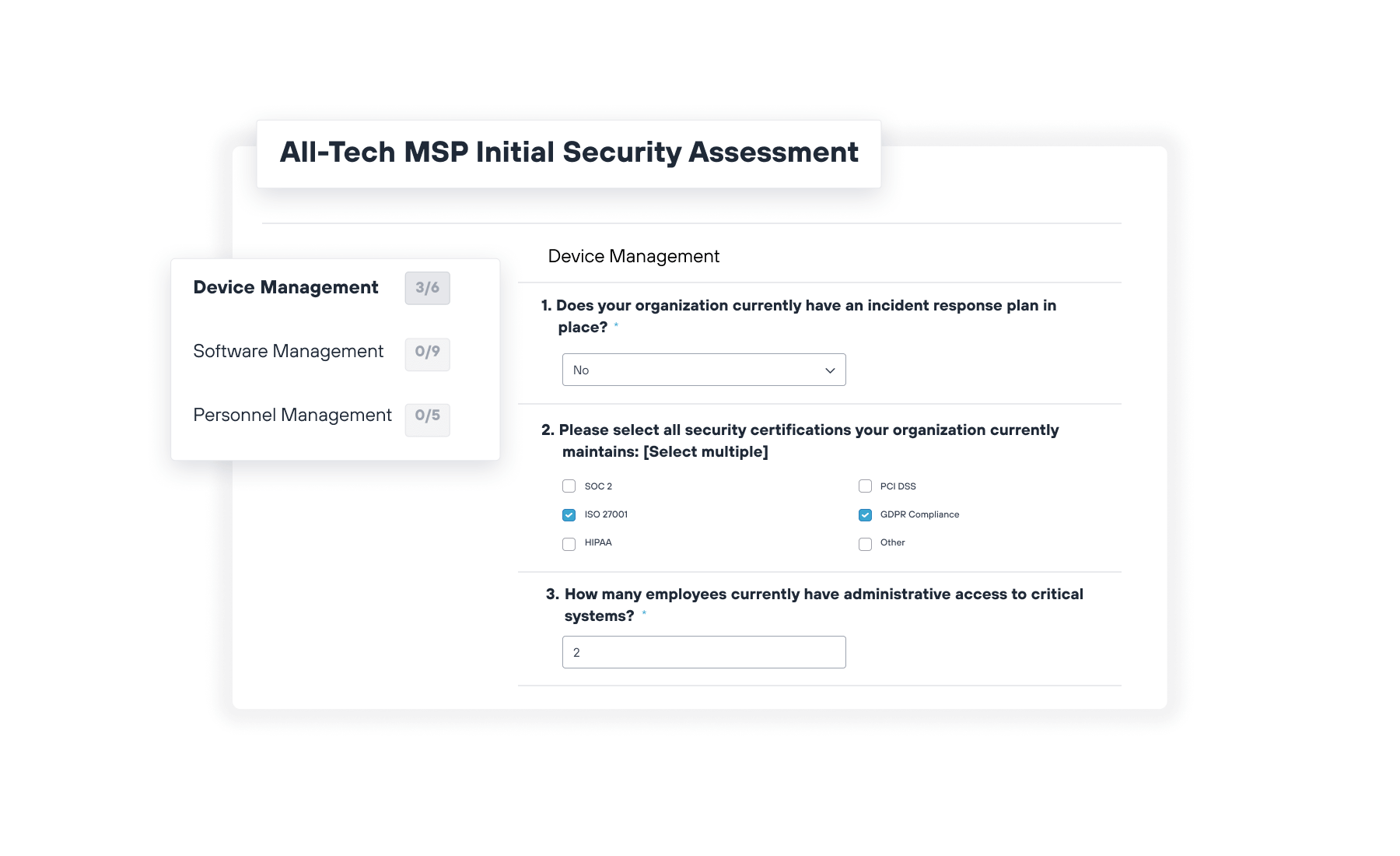
Fast and easy security assessments
Quickly analyze security, risk, and compliance postures with out-of-the-box and customizable assessments aligned to NIST CSF, CIS and more.
- Assess and document client and vendor security processes
- Identify and document critical coverage and process gaps
- Receive targeted recommendations for improvement
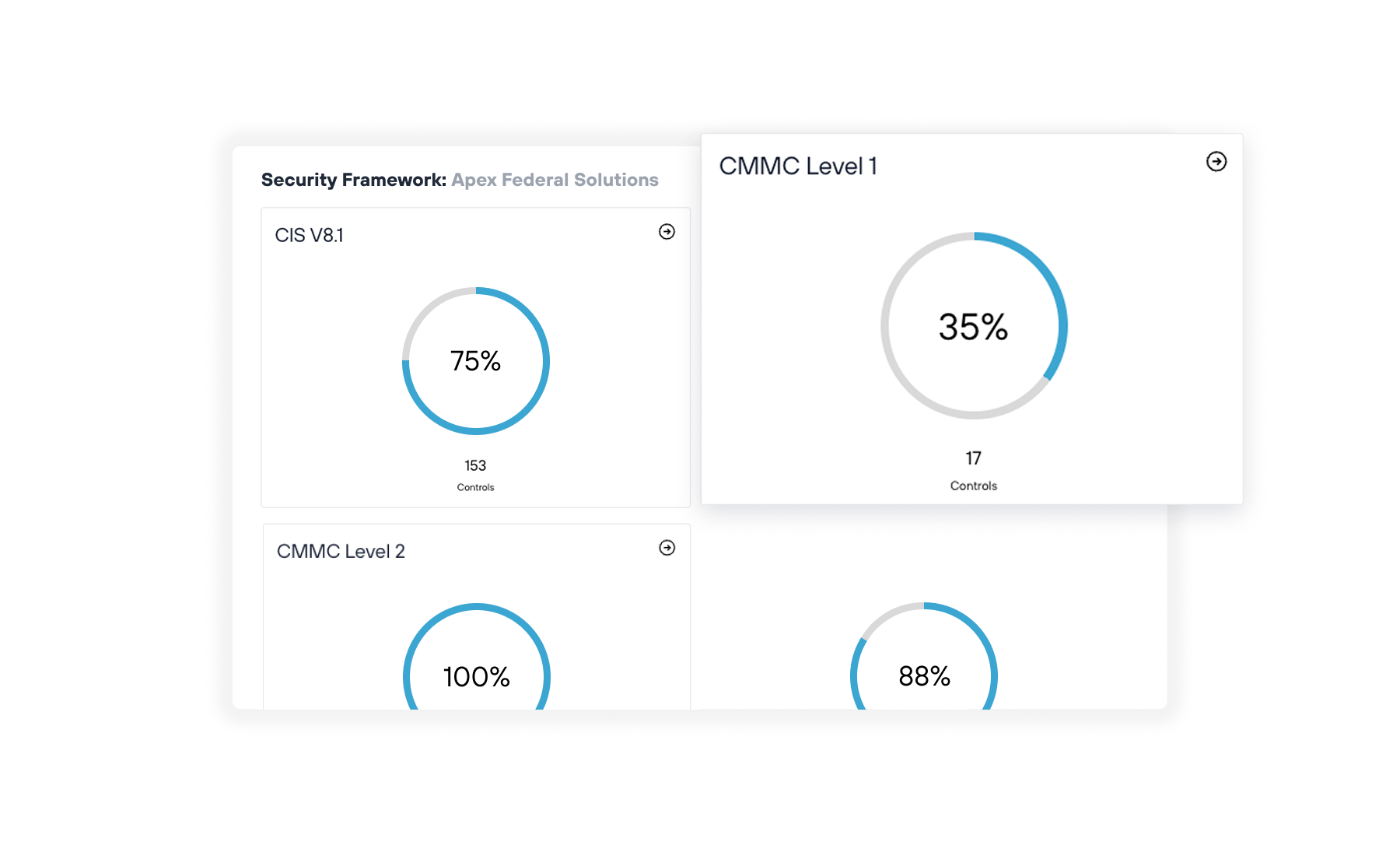
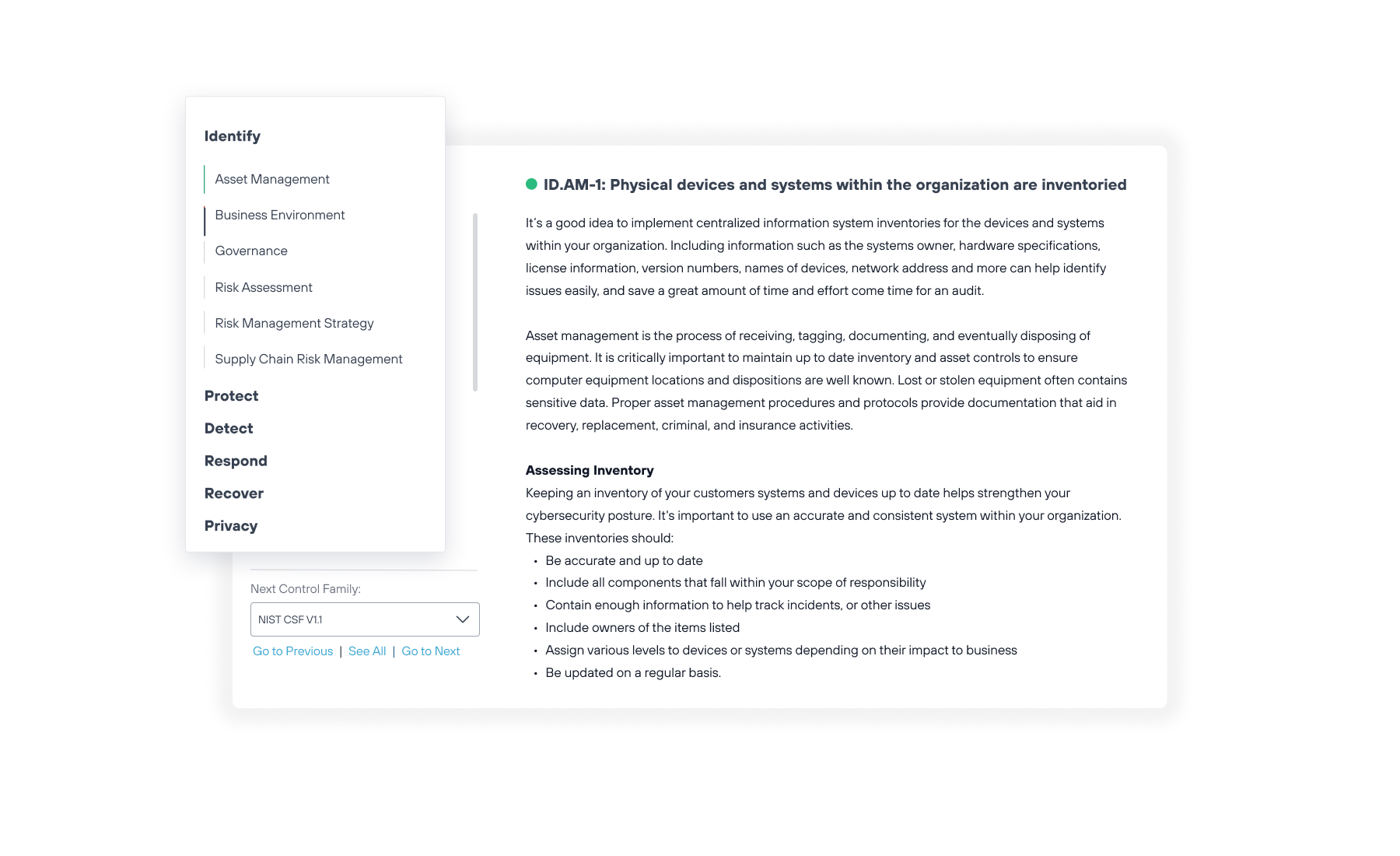
Simplified, comprehensive frameworks
Document and track client adherence to risk management and compliance frameworks like NIST CSF, CIS, CMMC, HIPAA, and more.
- Access expert-driven insights to understand scope
- Automatically map client security controls to known requirements
- Streamline audit reviews with a single source of truth
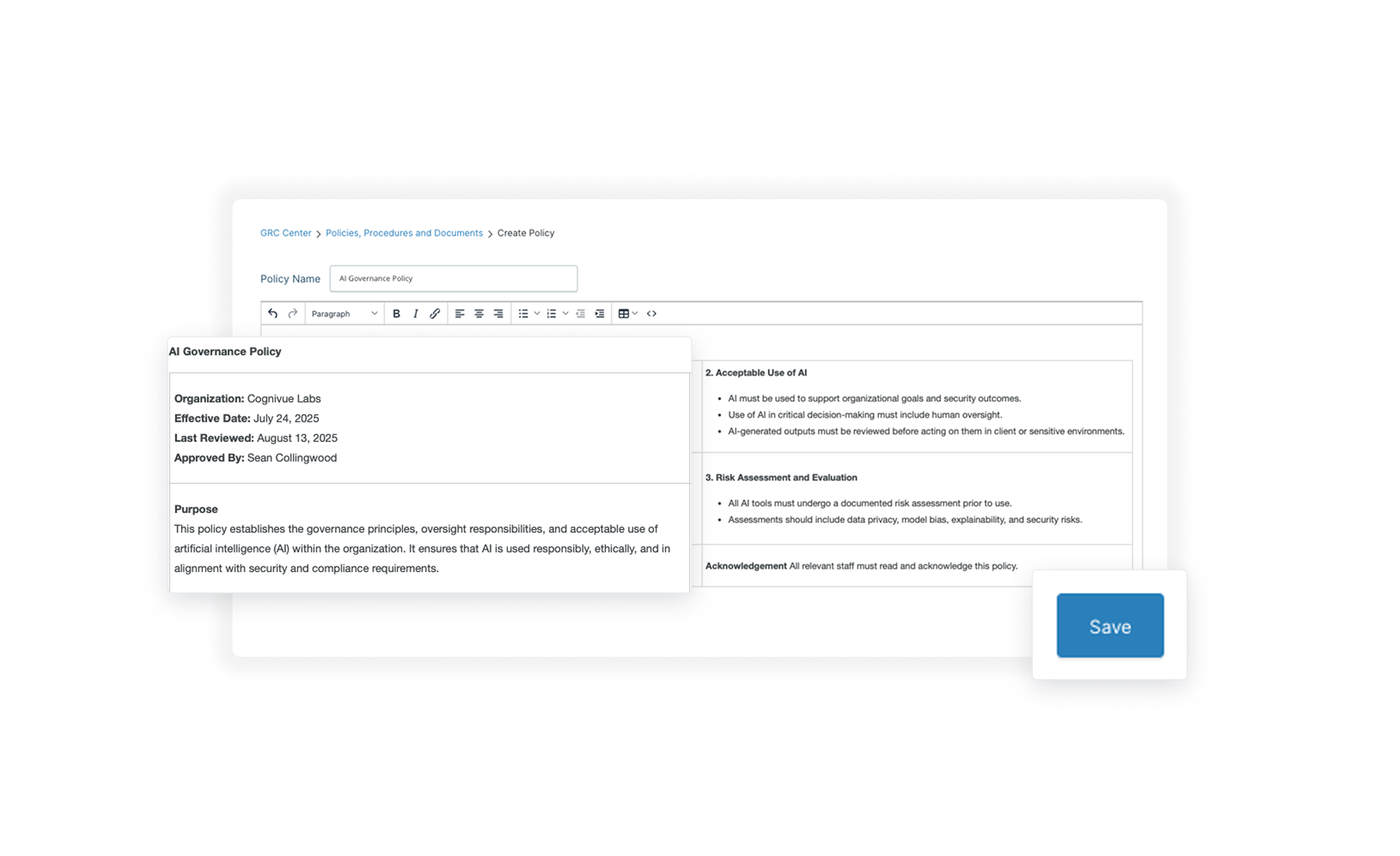
Consolidated policy documentation
Document all security, risk management, and compliance processes and procedures across all clients in a single integrated platform.
- Quickly access documented roles and responsibilities
- Connect clearly defined program goals with results
- Map repeatable organizational processes across tenants
Todyl Managed GRC
Todyl GRC makes it easy to understand organizational risk, meet and demonstrate continuous compliance, and follow cybersecurity best practices with extensive framework guidance, rapid security assessments, automated control mapping, centralized policy documentation, and more.
Simplified risk and compliance management
Todyl GRC makes it easy to assess and meet risk management and compliance with extensive embedded documentation, requirement scoping, policy attestation, and more:
- Comprehensive coverage of government and industry requirements
- Automated mapping to specific regulations and requirements
- Simple assessment and attestation tools for mapping compliance capabilities
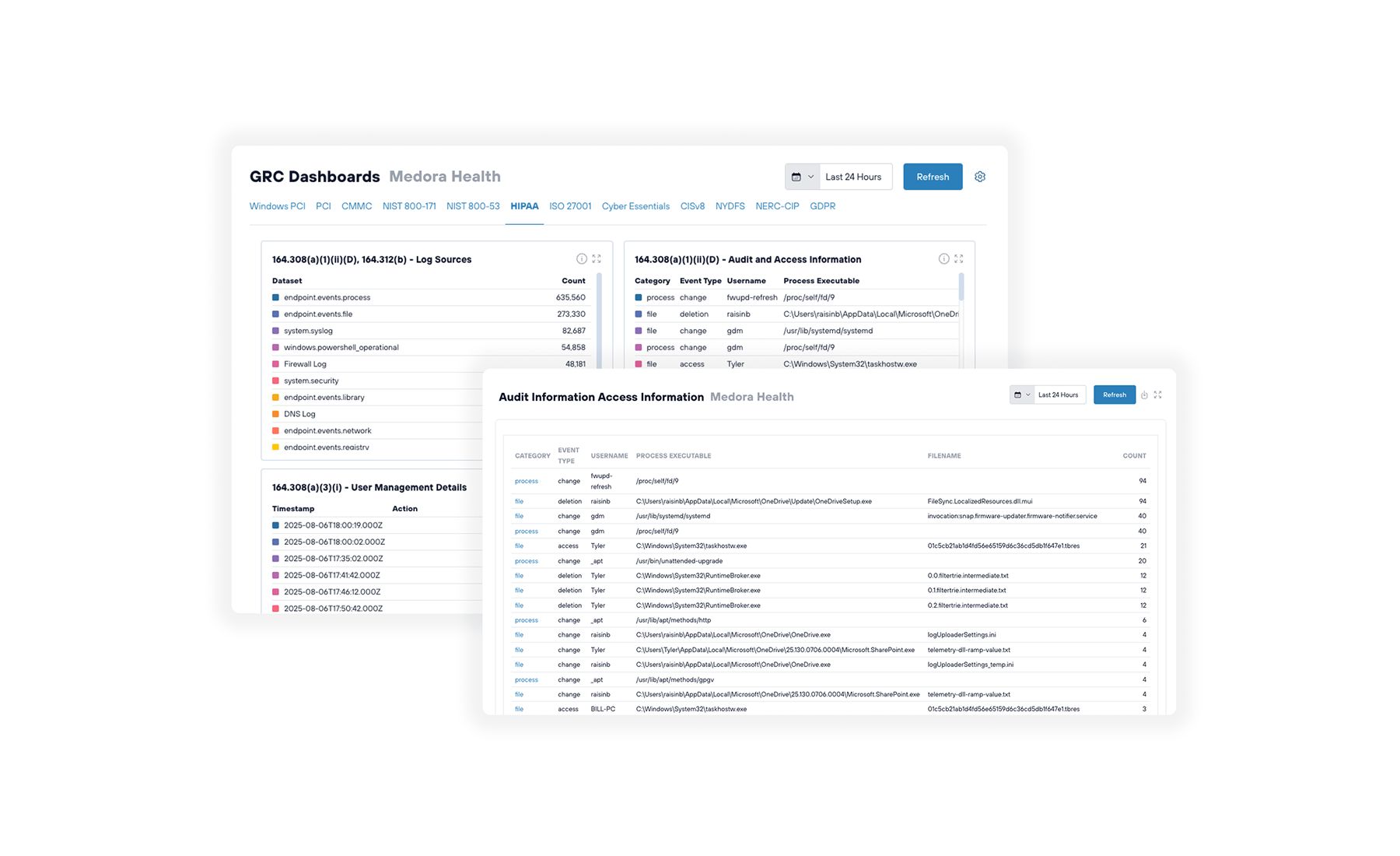
Comprehensive dashboards and reporting
An extensive library of expert content and native integration with Todyl Managed Cloud SIEM make demonstrating cybersecurity and compliance easy:
- Pre-defined and custom dashboards for relevant frameworks and regulations
- Expert-defined compliance insights and operating recommendations
- Single, intuitive interface for demonstrating and managing compliance
Streamlined cyber insurance and warranties
Todyl has existing certification agreements with cyber risk assessment partners like SPECTRA to provide easy access to cyber warranties and insurance policies:
- Rapid, no-fee certification process for qualified Todyl partners
- Marketplace access to A+ insurance policies and flexible cyber warranty tiers
- Streamlined claims processes for generating fast, no-hassle payouts
Enterprise GRC for any organization
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Suspendisse varius enim in eros elementum tristique. Duis cursus, mi quis viverra ornare, eros dolor interdum nulla, ut commodo diam libero vitae erat. Aenean faucibus nibh et justo cursus id rutrum lorem imperdiet. Nunc ut sem vitae risus tristique posuere.

Global network protection
Deliver secure connectivity for users, with lightning-fast speeds and unwavering reliability from anywhere in the world. Defend against attacks and boost productivity by:
- Detecting advanced threats
- Stopping unauthorized activity
- Blocking malicious traffic
- Smart traffic routing w/optional static IPs
- Maintaining seamless-operations for authorized users

Global network protection
Deliver secure connectivity for users, with lightning-fast speeds and unwavering reliability from anywhere in the world. Defend against attacks and boost productivity by:
- Detecting advanced threats
- Stopping unauthorized activity
- Blocking malicious traffic
- Smart traffic routing w/optional static IPs
- Maintaining seamless-operations for authorized users

Global network protection
Deliver secure connectivity for users, with lightning-fast speeds and unwavering reliability from anywhere in the world. Defend against attacks and boost productivity by:
- Detecting advanced threats
- Stopping unauthorized activity
- Blocking malicious traffic
- Smart traffic routing w/optional static IPs
- Maintaining seamless-operations for authorized users
Testimonials
GRC FAQs
What regulations does Todyl support?
Todyl supports a wide range of common regulations and security frameworks out-of-the-box, including CIS V8.1, CMMC, HIPAA, NIST CSF, NIST SP 800-171 Rev 3.0, and others. Additional regulations and frameworks are added on a continuous basis and can be added as needed.
What are Todyl Security Assessments based on?
Todyl’s Security Assessment is based on a series of critical controls and a set of actions that collectively form a defense-in-depth set of best practices that mitigate the most common attacks against systems and networks
Can I add my own operating policies?
Yes, GRC features a documentation repository where you can detail your policies and procedures and subsequently map them to known requirements of compliance regulations and frameworks within the GRC product.
How do I know which regulations my clients need to follow?
Todyl GRC’s Compliance Assistant allows you to ask a short series of demographic and business operations questions about each individual client that will then provide clear recommendations about which regulations they need to follow.
GRC Related Content
Get started with GRC today